Most small business owners believe they’re too small to be targeted for ransomware. The data says otherwise, and the stakes couldn’t be higher.
Let’s get one thing out of the way immediately: cybercriminals are not just targeting Microsoft, JPMorgan, or the NHS.
They’re targeting the bakery in Bengaluru that digitised its invoicing system last year. The 12-person marketing agency in Manchester that stores its client contracts in the cloud. The family-owned auto parts distributor in Chicago with 40 employees and a shared Google Workspace account.
They’re targeting you.
And in 2026, the scale of this targeting has reached a tipping point that every small and medium-sized business owner needs to understand, not tomorrow, not after the next budget cycle, but right now.
“Ransomware attacks jumped 34% in 2025 alone, and 88% of all ransomware breaches involved small and midsize businesses, not large enterprises.”, Verizon 2025 Data Breach Investigations Report
This isn’t a scare tactic. This is data. And in this post, we’re going to walk you through exactly what the numbers say, why hackers are deliberately choosing businesses like yours, what an attack actually costs, and what you can do about it before it’s too late.
The Numbers Don’t Lie, Ransomware Is Exploding
If you thought ransomware was someone else’s problem, consider the following statistics gathered from the most authoritative cybersecurity sources of 2025 and early 2026.
- 88% of all ransomware breaches in 2025 involved small and midsize businesses (Verizon DBIR 2025)
- 34% increase in ransomware attacks on small businesses between 2024 and 2025
- 5,010 ransomware incidents reported in the US alone in just the first 10 months of 2025, a 50% jump over 2024
- 45% overall surge in global ransomware attacks across 2025, with experts projecting 12,000+ incidents in 2026
- $5.08M global average total cost of a ransomware breach in 2025, including downtime, legal fees, and reputational damage
- 69% of businesses that paid a ransom were attacked again within the same year
Let that last one sink in. Paying the ransom doesn’t solve the problem, it makes you a repeat target.
The Verizon 2025 Data Breach Investigations Report found that ransomware was present in 44% of all breaches globally, a 37% increase from its 2024 report. For large organisations, ransomware appeared in 39% of breaches. For small and midsize businesses, that number was 88%. That’s not a rounding error. That’s a fundamental shift in who attackers are going after.
And the US isn’t alone. According to NordStellar research, the US accounted for 64% of all global ransomware cases in 2025. But Canada saw a 46% jump in incidents, and Germany saw a staggering 97% increase year-over-year. The UK Government’s Cyber Security Breaches Survey 2025 found that 43% of UK businesses experienced a cybersecurity breach or attack in the past year, that’s approximately 612,000 businesses.
In India, the picture is equally alarming. A Mumbai-based manufacturing SME suffered a devastating attack in January 2026, losing 12 days of production and spending ₹1.2 crore on recovery, legal fees, and reputation management, and that’s a relatively contained example.
Why Hackers Love Small Businesses (It’s Not Personal, It’s Business)

Here’s something counterintuitive: cybercriminals are not choosing small businesses by accident or out of desperation. They’re choosing them strategically. Ransomware gangs operate like businesses. They have payroll, project managers, customer service reps (yes, really, they have support teams to help victims ‘pay smoothly’), and they care about ROI.
And the ROI calculation on small businesses is compelling for them. Here’s why:
Reason 1: You Have Data Worth Stealing
Small businesses handle a goldmine of sensitive information: customer payment details, employee records, supplier contracts, healthcare data, financial accounts, and intellectual property. To a cybercriminal, a small business is like a convenience store, lower security than a bank vault, but still full of cash.
Reason 2: Your Defences Are Weak, By Default
According to Astra’s State of Continuous Pentesting Report 2025, only 14% of SMEs have adequate defences against advanced threats. 51% of small businesses use no IT security measures at all. 47% of businesses with fewer than 50 employees allocate zero budget to cybersecurity. And 36% of small business owners have no concern about cyberattacks, yet.
The most common factor contributing to ransomware success in 2026? Lack of expertise. The second most common? Security gaps that businesses already know about but haven’t fixed. That’s not a technology problem. That’s a governance problem.
Reason 3: AI Has Made Attacking You Cheaper Than Ever
Ransomware-as-a-Service (RaaS), where criminal gangs license their ransomware tools to affiliates, has industrialised cybercrime. New variants like FOG, Lynx, Cicada 3301, Dragonforce, and Frag emerged in 2025 specifically designed to target SMEs at scale. In Q2 2025, the Qilin group alone carried out 81 attacks in a single month, a 47.3% surge.
Meanwhile, AI tools allow attackers to craft hyper-personalised phishing emails at volume. An attacker can now research your business, your employees, your suppliers, and your clients, and write a convincing email impersonating any of them, in minutes. The human firewall that used to catch generic ‘Nigerian prince’ scams is crumbling against this level of sophistication.
Reason 4: You’re Part of a Bigger Supply Chain
Here’s the kicker that most SME owners don’t realise: even if your own data isn’t valuable enough to target directly, you might be a stepping stone. Attackers use SMEs as ‘island hopping’ targets, breaching a small supplier or vendor to gain access to the larger enterprise client they actually want. According to Cybereason, SMEs are most vulnerable to supply chain attacks for exactly this reason.
If you’re a vendor, partner, or service provider to any larger organisation, your security posture is their security problem too. And increasingly, large enterprises are auditing their SME suppliers, and dropping those who can’t demonstrate basic cyber hygiene.
How a Ransomware Attack Actually Works in 2026
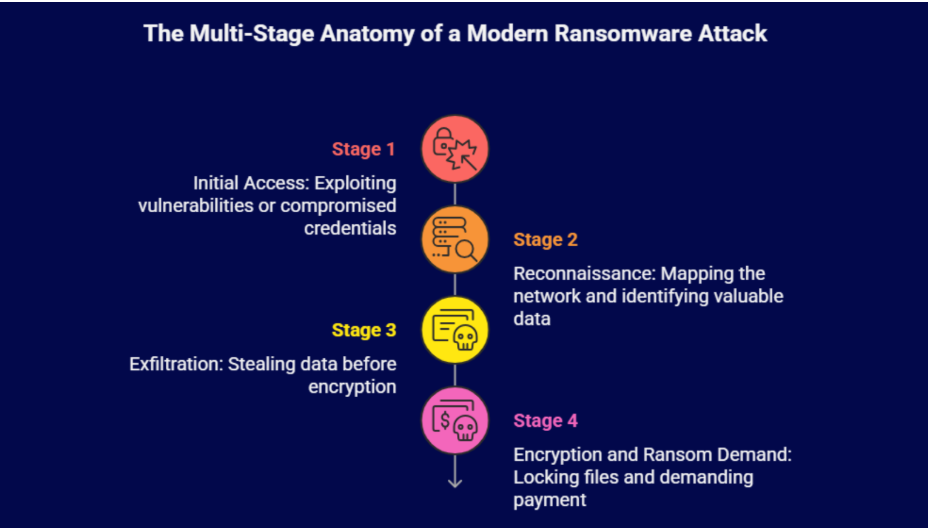
Understanding the anatomy of an attack helps you recognise and stop it before it’s too late. Modern ransomware doesn’t just encrypt your files and disappear. It’s sophisticated, multi-stage, and often running silently in your systems for days or weeks before you even know it’s there.
Stage 1: Initial Access, Getting In Through the Front Door
32% of ransomware incidents in 2025 started with exploited vulnerabilities, unpatched software, outdated operating systems, or misconfigured cloud applications. 23% started with compromised credentials, stolen usernames and passwords purchased from dark web marketplaces or obtained through phishing.
The most common entry points for SMEs include: exposed Remote Desktop Protocol (RDP) ports, weak or reused passwords, phishing emails with malicious attachments or links, unpatched third-party applications, and unsecured VPN access.
Stage 2: Reconnaissance, Mapping Your Business
Once inside, the attacker doesn’t immediately deploy ransomware. They explore. They map your network, identify your most valuable data, locate your backups, and elevate their privileges. Modern attacks can remain dormant for 24–72 hours, or even weeks, while this happens. This is why 57% of ransomware incidents in Q4 2024 were first detected by external parties, not the organisations themselves.
Stage 3: Exfiltration, Stealing Your Data First
This is what makes 2026 ransomware so much worse than what most people picture. 87% of ransomware attacks in 2025 involved data exfiltration, attackers stole a copy of your data before encrypting it. This creates what’s known as ‘double extortion’: even if you have backups and refuse to pay the ransom, they threaten to publish your sensitive data publicly unless you pay. Customer records. Employee details. Financial statements. Supplier contracts. All online, forever.
Stage 4: Encryption and Ransom Demand
Modern ransomware encrypts systems in under two hours once deployed. You wake up to find every file locked, a ransom note on every screen, and your business at a complete standstill. The average system remains offline for 24 days after a ransomware attack. For most small businesses, 24 hours of downtime is painful. 24 days is potentially fatal.
What It Actually Costs: Beyond the Ransom
When people think about ransomware costs, they fixate on the ransom payment. In reality, the ransom is often the smallest part of what you’ll spend. Here’s the full financial picture:
- Ransom payment (if paid): Median was $1 million in 2025, down from $2M in 2024, but still devastating for most SMEs
- Recovery costs (even if not paying): Average $1.53 million globally in 2025, excluding ransom, for SMEs specifically, costs ranged from $120,000 to $1.24 million
- Downtime: 24 days average without systems, lost productivity, missed orders, delayed deliveries, broken client relationships
- Legal fees and regulatory fines: GDPR (UK/EU), DPDPA (India), HIPAA (US), fines for data breaches can run into hundreds of thousands
- Reputational damage: 80% of SMEs that suffered a cyberattack had to spend significant time rebuilding trust with partners and clients
- Customer churn: Data breach announcements trigger customer cancellations that can take months or years to recover
- Cyber insurance premium increases: Post-attack, your premiums will rise, if you can get coverage at all
The IBM 2025 Cost of a Data Breach Report puts the global average total cost of a ransomware attack at $5.08 million. Mastercard’s global SME cybersecurity study found that nearly 1 in 5 SMEs that suffered a cyberattack filed for bankruptcy or were forced to close entirely.
If 75% of small businesses were to experience a ransomware attack, the majority would face bankruptcy shortly after., Industry research, 2025
And if you think cyber insurance is the safety net? Only 17% of small businesses currently carry cyber insurance. 48% of those who do buy it only purchased it after they were already attacked. And insurers are increasingly rejecting claims from businesses that failed to maintain basic security controls.
The 2026 Threat Landscape, What’s New and What’s Coming

The ransomware ecosystem of 2026 is fundamentally different from what it was even two years ago. Here’s what’s changed:
- AI-Powered Attacks Are the New Normal
Attackers now use generative AI to create customised phishing emails, automate reconnaissance, identify vulnerabilities, and even conduct negotiations. The 46% of SMEs reporting AI-generated phishing attacks in 2025 expect this number to grow significantly in 2026. The quality of deceptive emails has reached a level where even cybersecurity-trained staff struggle to distinguish them from legitimate communications.
- Ransomware Groups Are Multiplying and Specialising
In 2025, ransomware incidents could be traced to 134 different groups, a 30% increase from the 103 groups in 2024. When law enforcement takes down a major group, fragments regroup under new names. The Lynx group evolved into Sinobi. ALPHV/BlackCat morphed. Dragonforce surged 212.5% in activity. Qilin became the most active group by mid-2025 with 81 attacks in a single month.
These groups are also specialising. Some focus purely on healthcare. Others on manufacturing SMEs. Others on professional services. FOG ransomware was specifically identified as frequently targeting small businesses in 2025.
- Cloud and Backup Attacks Are Growing
A new threat called ‘Codefinger’ targeted AWS S3 buckets in 2025, making recovery impossible without payment even for organisations with cloud backups. Ransomware groups now prioritise finding and destroying backups as part of their attack sequence, eliminating your recovery options before you even know you’ve been hit. 1 in 3 SMEs discover their latest backup is unusable during an actual recovery attempt.
- Supply Chain Attacks Are Escalating
The PowerSchool attack in late 2024 compromised K-12 education data affecting millions of students. Ingram Micro, one of the world’s largest IT distributors, was hit by the SafePay ransomware group in July 2025. When large organisations are compromised through their supply chains, every SME vendor they work with comes under scrutiny, and sometimes, becomes the next target.
Your Action Plan, What to Do Right Now
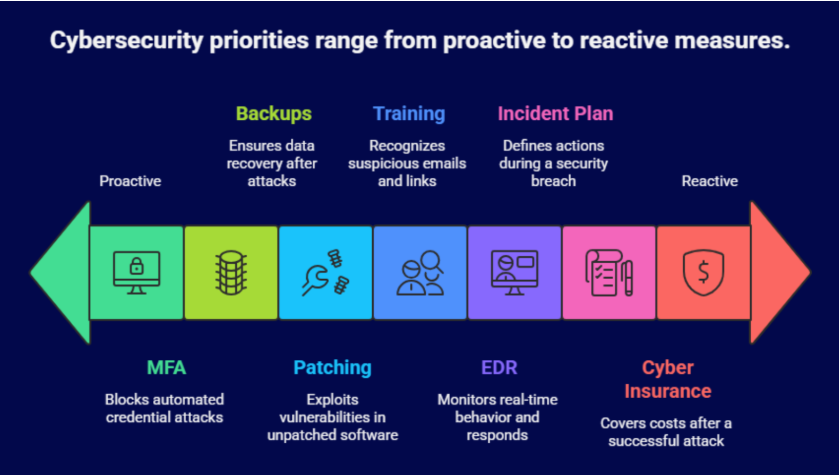
The good news, and there is good news, is that most ransomware attacks exploit known, preventable weaknesses. You don’t need an enterprise security budget to dramatically reduce your risk. You need discipline, consistency, and the right priorities.
Priority 1: Multi-Factor Authentication on Everything
MFA is the single most impactful step you can take. Enabling MFA blocks 99.9% of automated credential-based attacks. Yet most SMEs still don’t enforce it across all accounts. Start here. Enable MFA on email, cloud storage, accounting software, remote access, and any system that holds sensitive data. Do it this week.
Priority 2: The 3-2-1 Backup Rule, Implemented Correctly
Maintain 3 copies of critical data, on 2 different media types, with 1 copy stored offsite (and ideally, immutable, meaning attackers cannot alter or delete it). 62% of SMEs adopted immutable backups in 2025, but 38% still haven’t. Verify your backups regularly. 1 in 3 SMEs discover their backup is unusable only during an actual recovery attempt.
Priority 3: Patch Everything, Consistently
32% of ransomware attacks started with exploited vulnerabilities in unpatched software. Keep operating systems, applications, and network hardware updated. Prioritise internet-facing systems and actively exploited vulnerabilities first. If you can’t patch immediately, disable the vulnerable feature until you can.
Priority 4: Employee Security Training
95% of cybersecurity breaches involve human error. Your employees are both your greatest vulnerability and your greatest potential defence. Run phishing simulations. Train staff to recognise suspicious emails, links, and requests. Create a culture where reporting a suspicious email is celebrated, not embarrassed. Organisations with EDR solutions and trained staff prevented 87% of ransomware attempts in 2025.
Priority 5: Endpoint Detection and Response (EDR)
Traditional antivirus cannot stop modern ransomware. Invest in an EDR or XDR solution that provides real-time monitoring, behavioural analysis, and automated response. For SMEs without in-house IT teams, a Managed Detection and Response (MDR) service from a trusted security provider offers 24/7 monitoring without the cost of an internal security team.
Priority 6: Incident Response Plan
Know what you’ll do before it happens. An incident response plan should define: who gets notified first, who has authority to isolate systems, who communicates with clients and regulators, and who handles ransom negotiation (if it comes to that). Organisations with tested incident response plans recover 3x faster than those without.
Priority 7: Cyber Insurance, But Do It Right
Only 17% of small businesses carry cyber insurance. Review your policy carefully, insurers increasingly deny claims from businesses that failed to maintain documented security controls. Before buying, understand what the policy covers: ransom payments, business interruption, legal costs, notification costs, and regulatory fines.
A Special Note for SMEs in India, USA, and UK

For Indian SMEs
India’s rapid digital adoption, from UPI payments to cloud-first operations, has created a large attack surface. Indian SMEs are increasingly targeted both directly and as supply chain entry points.
The Digital Personal Data Protection Act (DPDPA) 2023 imposes significant obligations for data breach notification and protection. Non-compliance after a breach can multiply your costs significantly. Indian manufacturing SMEs, in particular, were identified as high-value targets by leading ransomware groups in 2025.
For US SMEs
The US remains the single largest ransomware target globally, accounting for 64% of all incidents. US ransomware incidents jumped 50% in 2025, with over 5,000 reported attacks in the first 10 months alone, and 85% of attacks are estimated to go unreported.
Sector-specific regulations (HIPAA for healthcare, FTC Safeguards Rule for financial services, state-level breach notification laws) add legal complexity to any ransomware incident. The FBI and CISA actively recommend against paying ransoms and provide free resources including the CISA Ransomware Guide.
For UK SMEs
43% of UK businesses experienced a cybersecurity breach or attack in 2025, approximately 612,000 businesses. Post-Brexit, the UK GDPR still imposes strict data protection obligations equivalent to EU GDPR.
The ICO (Information Commissioner’s Office) can issue fines of up to £17.5 million or 4% of global annual turnover for significant data breaches. The UK’s National Cyber Security Centre (NCSC) offers free Cyber Essentials certification, a recognised baseline that can also reduce your cyber insurance premiums.
Final Word: The Cost of Waiting
The most dangerous sentence in cybersecurity is: ‘We haven’t been attacked yet, so we’re probably fine.’
In 2026, that’s not a security strategy. That’s hope. And hope is not a defence against ransomware.
The data is unambiguous: SMEs are the number one target, attacks are accelerating, the tools to attack you are cheaper and more powerful than ever, and the cost of an incident, financial, operational, and reputational, can end your business.
But here’s the other truth: the attackers are going for easy targets. They’re looking for the businesses with no MFA, unpatched systems, untrained staff, and no backup plan. Every hour you invest in your cyber defences moves you off that list and onto the ‘too much trouble’ pile.
You don’t need to be perfect. You need to be harder to attack than the business next door.
Don’t let your business become another ransomware statistic. Book a vulnerability audit today and find out exactly where you’re exposed, before an attacker does.
Frequently Asked Questions
1. Why are small businesses targeted by ransomware?
Small businesses are targeted because they often have valuable data but weaker security. Unlike large enterprises, many SMEs lack dedicated cybersecurity teams, making them easier to breach. Attackers see them as high-ROI targets with lower resistance and higher chances of ransom payment.
2. What is the most common way ransomware attacks start?
Most ransomware attacks begin through phishing emails, stolen credentials, or unpatched vulnerabilities. Attackers trick employees into clicking malicious links or exploit outdated software. Weak passwords and exposed remote access systems like RDP are also major entry points for SMEs.
3. Can a small business recover from a ransomware attack without paying?
Yes, but only if proper backups and security controls are in place. Businesses with secure, tested, and isolated backups can restore systems without paying. However, if data is also stolen (double extortion), recovery becomes more complex due to potential data leaks.
4. How much does a ransomware attack cost a small business?
The cost goes far beyond the ransom. SMEs typically face ₹1 lakh to ₹10+ crore (or $120K–$1M+) in recovery costs, including downtime, legal fees, lost revenue, and reputational damage. In severe cases, attacks can lead to business closure.
5. What are the best ways to prevent ransomware attacks in 2026?
The most effective prevention steps include:
- Enabling multi-factor authentication (MFA) everywhere
- Maintaining secure, offline or immutable backups
- Keeping systems patched and updated
- Training employees against phishing attacks
- Using EDR/XDR security tools for real-time monitoring
Consistent implementation of these basics can stop the majority of ransomware attacks.