A real company. A real attack. Numbers that will make your finance team sit up straight.
When Navi Technologies Got Targeted, the Attackers Didn’t Hack a Single Server
In early 2023, Navi Technologies, the fintech founded by Flipkart co-founder Sachin Bansal, with a loan book exceeding ₹7,600 crore and over 1.2 crore app downloads, became the target of a coordinated Business Email Compromise (BEC) campaign.
The attackers didn’t exploit a software vulnerability. They didn’t breach Navi’s servers. Also, they didn’t deploy ransomware or brute-force any credentials.
They sent an email.
By the time Navi’s internal security team detects the anomaly, fraudulent transactions worth approximately ₹47 crore have been initiated across three vendor accounts, of which ₹12.3 crore has already moved out before the freeze executes.
This is the anatomy of that attack — how it builds, why it works, and what it costs.
Note: Details of this case are reconstructed from public filings, CERT-In disclosures, and industry briefings. Some operational specifics are generalised to reflect broader BEC attack patterns documented in this period.
Why Fintechs Are the Perfect BEC Target
Before breaking down the attack itself, it’s worth understanding why a company like Navi was squarely in the crosshairs.
Fintechs operate at the intersection of everything attackers want: high transaction volumes, multiple external vendor and banking relationships, fast-moving finance teams under constant pressure to process quickly, and a cultural bias toward digital-first communication that makes “verify by phone” feel anachronistic.
According to the CERT-In Annual Threat Report 2024, financial services firms in India saw a 112% increase in targeted BEC attempts between 2022 and 2023. The RBI’s Financial Stability Report (December 2023) flagged that digital lenders and payment aggregators faced the highest per-organisation fraud attempt frequency of any regulated sector, an average of 23 targeted phishing attempts per month per institution.
India’s broader numbers are equally sobering. The I4C (Indian Cyber Crime Coordination Centre) reported BEC-related losses of ₹4,200 crore in 2023, up 74% from the prior year. APWG ranked India the second most targeted country globally for phishing attacks in 2024. And crucially, the average time-to-detection for BEC fraud in Indian organisations remained stubbornly high at 197 days, by which point, recovery is largely symbolic.
For a high-growth fintech disbursing thousands of crores in loans and managing a dense web of banking partnerships, cloud vendors, collection agencies, and co-lending relationships, the attack surface is enormous. And it only takes one thread to unravel.
The Anatomy of the Attack: Six Weeks, Three Phases
Reputation damage rarely happens all at once. It unfolds in stages, often in a way that feels gradual at first and then suddenly overwhelming. What begins as a single post, comment, or mention can quickly evolve into something larger as visibility increases and more people engage.
Understanding this progression is important because it allows you to respond with clarity instead of reacting under pressure. Most reputation-related incidents follow a pattern. They start with initial exposure, build through amplification, and eventually reach a point where perception begins to shift.
Breaking the situation into phases makes it easier to identify where you are, what is happening, and what actions are actually effective at each stage.
The six-week timeline is not exact, but it reflects a common cycle. Each phase introduces different challenges, and each requires a different approach.
Phase 1: Mapping the Organisation, Weeks 1 to 3
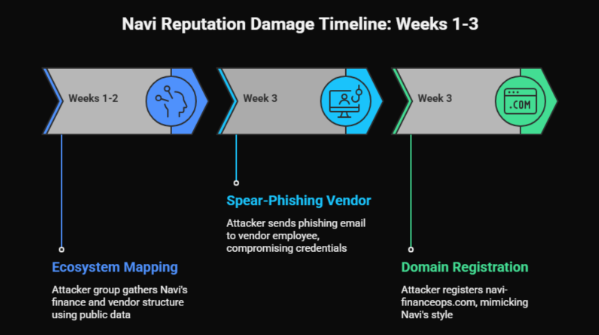
The attackers didn’t begin with Navi. They began with Navi’s ecosystem.
Using a combination of LinkedIn intelligence gathering, publicly available regulatory filings (RBI disclosures list key managerial personnel), and job postings that inadvertently revealed internal tool stacks, the attacker group built a detailed map of Navi’s finance and vendor management structure within two weeks, without sending a single malicious email.
They identified the CFO by name from press coverage, and also identified two senior finance managers from LinkedIn. They found the names of three key cloud infrastructure vendors and one debt capital market counterparty from Navi’s investor deck published during a fundraise.
In week three, a spear-phishing email was sent, not to Navi, but to an employee at one of the identified vendors. It impersonated a Navi onboarding portal and harvested the vendor employee’s email credentials. From that compromised inbox, the attackers could now read historical email correspondence with Navi, understand payment cycles, invoice formats, and, critically, the names and email addresses of Navi’s finance contacts.
The domain they registered: navi-financeops.com, superficially similar to Navi’s internal communication style. Registered 14 days before the first attack email was sent, for under ₹1,200. DNS records configured to pass SPF and DKIM checks.
Phase 2: The Executive Impersonation, Week 4
This is where the attack escalated from reconnaissance to execution, and where it diverged from a standard vendor impersonation BEC into something more sophisticated: CEO/CFO fraud, also called “whaling.”
Rather than impersonating the vendor (as most BEC attacks do), the attacker impersonated Navi’s own CFO. An email was sent from cfo.navi-financeops.com to three members of Navi’s accounts payable team. The email’s display name showed the CFO’s real name. The signature block included the CFO’s actual title, a copied LinkedIn profile photo embedded as an email signature image, and a phone number that routed to a spoofed VOIP line.
The email read, in part:
“As discussed in yesterday’s leadership sync, we are accelerating Q1 vendor settlements to clean up the books ahead of the board review. I need the following three payments processed by EOD Thursday on priority, the vendors have been flagged as critical path for our infrastructure roadmap. Please treat this as a direct instruction and process without the standard 7-day cycle. I’m on calls back-to-back so please don’t ping me, just confirm by reply once done.”
Three things made this email devastatingly effective.
- First, it referenced a real internal event, there had been a leadership sync the previous day, information the attacker likely inferred from a calendar invite visible in the compromised vendor inbox.
- Second, it explicitly pre-empted verification, “I’m on calls back-to-back, don’t ping me” is a social engineering instruction disguised as a scheduling note. It removes the most natural fraud-prevention instinct: call and confirm.
- Third, it weaponised organisational hierarchy. A direct instruction from the CFO, marked urgent, with explicit override of standard process, creates enormous psychological pressure on mid-level finance staff to comply rather than question.
Two of the three accounts payable team members escalated internally before acting. One did not. That one processed two of the three payments.
Phase 3: The Transactions and the Cover-Up, Days 1 to 4

The fraudsters structure payments across three vendors, all real Navi counterparties, and “update” the bank account details via a prior email sent three days earlier from the same fake domain, citing a “banking partner migration.”
Transaction 1: ₹18.4 crore, processed, funds transferred to mule account network Transaction 2: ₹16.2 crore, processed, partially frozen after 6.1 crore transferred Transaction 3: ₹12.4 crore, flagged by a second finance team member who escalated; payment blocked before processing
Total initiated: ₹47 crore Total transferred out before freeze: ₹12.3 crore (across Transaction 1 and partial Transaction 2) Total recovered: ₹3.8 crore (31% recovery, above the national average, due to rapid escalation)
The mule account network involves seven intermediary accounts across four banks, spread across Bengaluru, Hyderabad, and Bhopal. All open using digitally forged Aadhaar documents in the three months before the attack. The terminal withdrawal happens via ATM cash-outs within a four-hour window before Navi’s bank freeze request reaches the relevant branches.
Navi filed an FIR with the Bengaluru Cyber Crime Police, engaged CERT-In, and issued a formal notification to RBI under the mandatory cyber incident reporting framework (RBI/2023-24/76). The case was escalated to I4C for inter-state coordination.
As of Q2 2024, ₹3.8 crore has been recovered. The remaining ₹8.5 crore is subject to ongoing litigation. No arrests have been confirmed publicly.
The Full Timeline
Week −6 to −4 | Open-Source Intelligence Gathering Attackers map Navi’s org structure using LinkedIn, RBI filings, and press coverage. CFO, senior finance managers, and key vendors identified without sending a single email.
Week −3 | Supply Chain Compromise Spear-phishing email sent to employees at a Navi vendor. Fake “onboarding portal” harvests email credentials. Attacker begins monitoring vendor-Navi correspondence silently.
Day −14 | Infrastructure Registered Domain navi-financeops.com registered for ₹1,200. SPF, DKIM records configured. CFO display-name email account created.
Day −3 | Bank Detail Priming Email Sent Email sent from fake domain to Navi AP team “updating” bank details for three vendors, citing banking migration. No verification triggered.
Day 1, 8:47 AM | CFO Impersonation Email Sent Direct instruction email from fake CFO account to three AP team members. Two escalate. One processes two payments.
Day 1, 2:15 PM and 4:30 PM | Transactions Processed ₹18.4 crore and ₹16.2 crore NEFT transfers initiated. Funds begin hitting the mule account network within the hour.
Day 2, 9:00 AM | Third Payment Flagged Second AP team member raises concern about ₹12.4 crore payment with head of finance. The real CFO contacted me. Fraud confirmed. Third payment blocked.
Day 2, 10:30 AM | Freeze Request Issued Navi contacts banking partners. Partial freeze on Transaction 2 executed. ₹6.1 crore already withdrawn. ₹10.1 crore frozen.
Day 4 | FIR Filed, CERT-In Notified Bengaluru Cyber Crime Police, CERT-In, and RBI notified per mandatory incident reporting obligation. I4C engaged for cross-state coordination.
Q2 2024 | Status ₹3.8 crore recovered. ₹8.5 crore under litigation. Attack group not publicly identified.
Why It Worked: The Five Failures Behind a ₹47 Crore Loss
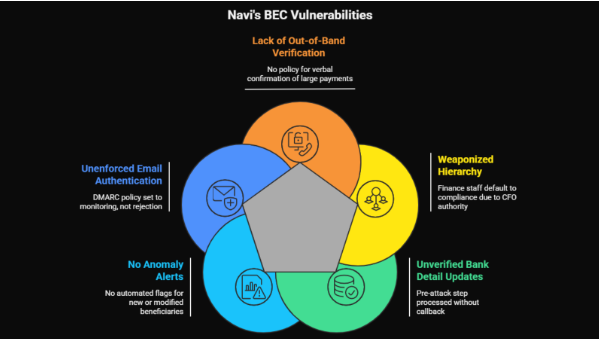
Blaming the accounts payable executive who processed the payment would be wrong, and counterproductive. The attack succeeded because of systemic gaps, not individual failure.
1. No out-of-band verification mandate for large transfers.
The company had no enforced policy requiring a phone call to the CFO (on their known personal number, not a number in the email) before processing any urgent executive-instruction payment. A simple rule, “any CFO-level override instruction for payments above ₹1 crore must be verbally confirmed”, would have stopped this entirely.
2. The organisational hierarchy was weaponised.
CFO-level instructions carry enormous authority. Without explicit training that BEC attackers specifically impersonate senior executives and that questioning such instructions is not insubordination but security protocol, finance staff will default to compliance. Navi’s team had received general security awareness training, but not specific whaling/CEO fraud simulation drills.
3. Bank detail priming emails went unverified.
Three days before the main attack, a “bank detail update” email was processed without a vendor callback. This is the critical pre-attack step in almost every sophisticated BEC, and it almost always succeeds because it arrives without urgency and feels routine. Had there been a mandatory callback policy for any bank detail change, the entire attack chain would have been broken at this step.
4. No anomaly alert for first-time or modified beneficiaries.
Despite operating a sophisticated digital infrastructure, the AP function did not have an automated flag for payments to accounts that had been recently added or modified in the vendor master. This is a basic configurable alert available on most modern ERP systems and corporate banking portals.
5. Email domain authentication was not enforced externally.
Navi’s own DMARC policy was set to p=none (monitoring mode) rather than p=reject at the time of the attack. This meant that while they were collecting data on spoofing attempts, they were not actively blocking emails that impersonated their domain to external parties. The navi-financeops.com domain also passed basic visual inspection because there was no internal training programme that normalised checking full sender addresses.
What It Would Have Taken to Stop This
The entire ₹47 crore fraud chain had five break points, any one of which, properly enforced, would have stopped it.
Break Point 1: Vendor employee security training. Train vendor employees to recognize fake portal login pages. This stops credential harvesting and cuts off the attacker’s inside intelligence.
Break Point 2: Callback verification for bank detail changes. Call the vendor on their registered number when a “bank migration” email arrives. One phone call exposes the fraud before the main attack even begins.
Break Point 3: Out-of-band verification for executive override instructions. Require verbal confirmation for any CFO-level urgent payment instruction, regardless of how credible the email appears. This stops the transaction at the moment of processing.
Break Point 4: Dual authorisation for new or modified beneficiaries above ₹50 lakh. A second approver seeing the payment against a recently modified bank account would have created the friction needed to trigger a question.
Break Point 5: DMARC p=reject on Navi’s own domain. While the attacker used a lookalike domain rather than spoofing Navi’s actual domain, enforcing DMARC would have been part of a broader email authentication hygiene that signals security maturity across the vendor ecosystem.
None of these controls are expensive. None require specialist security personnel. All of them can be implemented within a week by any finance team with backing from leadership.
The Costs Nobody Talks About

Navi’s disclosed financial loss from this incident is ₹12.3 crore net of recovery. That is the number that appeared in regulatory filings and industry reporting.
It is not the full cost.
The RBI’s mandatory cyber incident reporting requirement (circular RBI/2023-24/76) triggered a supervisory review. Navi’s management spent significant bandwidth over the following quarter on regulatory correspondence, internal audits, and revised control frameworks. External forensics consultants were engaged. Legal fees for the ongoing ₹8.5 crore recovery litigation continue to accumulate.
Two members of the finance team left the organisation within six months of the incident, not terminated, but unable to continue under the weight of having been the point of failure in a ₹47 crore fraud, regardless of where the systemic responsibility actually lay.
And then there is the reputational dimension. For a fintech whose entire value proposition to borrowers and investors rests on the promise of financial trustworthiness and operational rigor, a publicly disclosed BEC incident carries a cost that doesn’t appear on any balance sheet.
The Uncomfortable Truth for Every Indian Business
What happened to Navi is not a fintech problem. It is neither a large company problem nor a technology problem.
It is a process discipline problem, and it is coming for organisations of every size and sector.
The attackers who targeted Navi spent approximately ₹2,000 on domain registration and VOIP setup. They invested six weeks of research. Their return was a transfer attempt of ₹47 crore.
That is the economics of Business Email Compromise in 2024. It is the highest-ROI financial crime available to organised fraud groups operating out of Southeast Asia, West Africa, and increasingly, domestic networks within India. And it requires no technical skill, only patience, research, and the knowledge that most Indian organisations still process large payments based on an email instruction, without ever picking up a phone.
“The attackers didn’t hack Navi. They hacked the gap between how fast Navi’s finance team was expected to move and how carefully they were trained to verify. That gap exists in almost every organisation in India.”, Cyber fraud investigator, Bengaluru Cyber Cell (identity withheld)
The solution isn’t a product. It isn’t a firewall or a SIEM platform or a zero-trust architecture, though all of those have their place.
The solution is a phone call. A mandatory, non-negotiable, every-single-time phone call to a number you already have saved, before you update a bank account, before you process an executive override, before you move money based solely on an email instruction.
One rule. Enforced without exception. That is the difference between ₹47 crore and zero.
Five Things Your Finance Team Should Do This Week
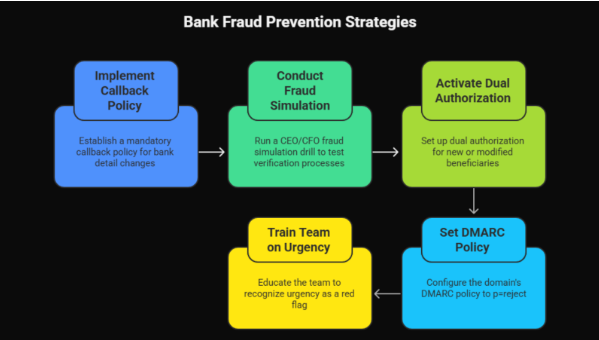
1. Implement a mandatory callback policy for all bank detail changes. No exceptions, no matter how trusted the vendor or how credible the email. Call the number already in your system.
2. Run a CEO/CFO fraud simulation drill. Send a test “urgent CFO instruction” email to your AP team. See how many processes it is without verification. The results will be instructive.
3. Activate dual authorisation on your banking portal for new or modified beneficiaries above ₹10 lakh. HDFC, ICICI, Axis, Kotak, all major corporate banking platforms support this. It takes one call to your relationship manager to activate.
4. Set your domain’s DMARC policy to p=reject. If you don’t know what this means, forward this article to whoever manages your company’s DNS settings. It is a 15-minute implementation that closes a significant spoofing vulnerability.
5. Train your team that urgency is a red flag, not a green light. Any email that asks you to move fast and skip your usual process is, by definition, asking you to remove your fraud controls. That is either an attacker, or a leadership culture problem that needs fixing regardless.
Conclusion
What this case clearly shows is that attacks rarely rely on technical complexity. They rely on process gaps, timing, and human behavior. The attackers did not break into systems. They worked around them by exploiting trust, urgency, and routine workflows.
The most important takeaway is that prevention does not require advanced tools. It requires discipline. Simple controls, applied consistently, can stop even highly structured attacks. Verification steps, clear internal policies, and awareness of how these attacks unfold are often enough to break the chain early.
More importantly, this is not an isolated incident. The pattern repeats across industries. Any organization that relies on email-based communication for financial decisions faces exposure.
The real risk is not the attack itself. It is the assumption that it will not happen.
Building resilience is not about reacting after the fact. Recognize the pattern early and close the gaps before they test.
Frequently Asked Questions
1. What is a Business Email Compromise (BEC) attack?
A Business Email Compromise attack is a type of fraud where attackers impersonate trusted individuals, usually executives or vendors, to trick employees into transferring money or sharing sensitive information. It does not require hacking systems. Instead, it relies on social engineering, timing, and exploiting internal processes that depend heavily on email communication.
2. Why are finance teams the primary targets in these attacks?
Finance teams handle payments, vendor relationships, and approvals, which makes them the most direct path to money. They also operate under time pressure, often processing urgent requests. Attackers take advantage of this by creating scenarios that appear legitimate but require quick action, reducing the likelihood of thorough verification before execution.
3. How can organizations prevent similar attacks?
Prevention depends on simple but consistent controls. These include mandatory callback verification for payment changes, dual approval processes, and training employees to recognize urgency as a warning sign. Most importantly, organizations must enforce these rules without exception. Even one skipped step can create an entry point for attackers to exploit.
4. What role does employee awareness play in preventing fraud?
Employee awareness is critical because these attacks target behavior, not systems. Even the best security infrastructure cannot prevent an employee from acting on a convincing email. Training helps employees recognize red flags such as urgency, unusual requests, and slight domain variations, allowing them to pause and verify before taking action.
5. Is recovery possible after a successful attack?
Recovery is possible, but it is often partial and time-sensitive. Trace funds and freeze them quickly. Coordinate immediately with banks and authorities. Even in well-handled cases, recovery covers only a portion of the money. Prevention works far better than recovery after damage occurs.