Picture a medieval castle. Thick walls. A drawbridge. A moat. Anyone inside those walls is trusted, they made it past the defences, so they must be one of us. Anyone outside? Suspicious.
For decades, this is exactly how corporate cybersecurity worked. Build a strong perimeter, a firewall, a VPN, maybe a login screen, and assume that anyone already inside the network is safe. The thinking was simple: if you got through the gate, you belong here.
That thinking is now catastrophically out of date.
Your data isn’t inside the castle anymore. It’s in Google Workspace, in AWS, in Microsoft 365, in your CRM, in your payroll software, accessed by employees in Mumbai, Dubai, and Singapore, on laptops at home, on phones at airports, through shared devices at co-working spaces. The castle walls you built don’t surround any of that. They surround nothing.
This is where Zero Trust Architecture comes in, and why it has rapidly become the most important security framework of our time.
What Exactly Is Zero Trust Architecture?
Zero Trust Architecture (ZTA) is a modern cybersecurity framework built on a foundational principle: never trust, always verify. Unlike traditional security models that assume everything inside the perimeter is safe, ZTA treats every user, device, and application as untrusted by default, whether inside or outside the network.
This approach continuously authenticates and authorises every access request, minimising the attack surface, preventing lateral movement, and protecting critical assets in a highly distributed digital environment.
The name can be a little misleading. Zero Trust doesn’t mean you trust nobody forever. It means you don’t grant trust automatically, it must be earned, proved, and continuously re-verified for every single interaction.
First conceptualised in 2009 by Forrester’s John Kindervag, Zero Trust has evolved into a prescribed way of being for organisations to maximise their security posture. It assumes some degree of compromise will occur, so no system, user, or asset should be implicitly trusted. This mindset helps limit the damage of breaches by reducing detection, response, and mitigation timelines and preventing lateral movement within the network.
Think of it this way: in a traditional security model, once you show your badge at the front door of a building, you can roam freely through every corridor, office, and server room.
Zero Trust says that even if you’ve shown your badge, you still need to verify your identity at every door, every room, every cabinet, and you only get access to the exact room you need, for the exact time you need it.
The Three Non-Negotiable Principles
Every Zero Trust implementation, regardless of size or complexity, is built on three core principles. These aren’t optional. They’re the philosophical DNA of the entire model.
Principle 1: Never Trust, Always Verify
The principle of “never trust, always verify” means that no user or device should gain access to resources solely based on their position inside a network or organisational boundaries. Traditional models often assign implicit trust to insiders, but zero trust eliminates this assumption.
Every access request, regardless of where it originates, is subject to identity, device, and access context checks. Even employees working onsite must authenticate and authorise their actions every time they interact with critical systems.
This is a radical departure from how most organisations have operated for 30 years. The “trusted insider” assumption has been the cause of some of the most devastating breaches in history, from the Edward Snowden incident to countless ransomware attacks where a single compromised employee account gave attackers unfettered access to entire networks.
Principle 2: Least Privilege Access
Grant only the minimum access required to complete a specific task, and only for the minimum time needed. A marketing executive doesn’t need access to the finance database. A customer service agent doesn’t need access to source code repositories. A contractor brought in for two weeks doesn’t need permanent credentials that work for two years.
Zero Trust operates under the assumption that a breach is not a possibility but an inevitability. This “assume breach” mentality forces security teams to design controls that can contain threats that have already bypassed initial defences.
Instead of focusing solely on perimeter prevention, the focus shifts to internal monitoring, threat detection, and rapid response to stop lateral movement and minimise the impact of a breach.
Least privilege is what makes “assume breach” survivable. If an attacker compromises one account, they can only access what that account could access, not everything.
Principle 3: Assume Breach
The “assume breach” principle encourages organisations to invest in threat detection, endpoint security, and segmented architectures that make infiltration and lateral movement extremely challenging. By expecting and planning for compromise, organisations can reduce the window between initial intrusion and detection, minimising potential fallout.
This principle is psychologically uncomfortable for many organisations, but it’s the most honest assessment of modern cyber risk. You will be targeted. You may be breached. The question is: when that happens, how quickly do you detect it, and how limited is the damage?
Why Is Zero Trust So Urgent Right Now?
You might be wondering: if Zero Trust was conceptualised in 2009, why is everyone talking about it so urgently in 2026? The answer is that the threat landscape and the working environment have both changed beyond recognition.
The proliferation of cloud computing, mobile device use, and the Internet of Things has dissolved conventional network boundaries. The workforce is more distributed, with remote workers who need access to resources anytime, anywhere, and on any device.
Consider what “normal” looks like for most organisations today in India, UAE, or Singapore:
Your employees work from the office, from home, from client sites, and while travelling. They use company laptops, personal phones, and shared devices. Your data lives in cloud platforms, SaaS applications, and third-party services. Your supply chain includes vendors, contractors, and partners who need access to some of your systems. And cyber threats, powered by AI, automated by ransomware-as-a-service gangs, delivered through increasingly convincing phishing, are more sophisticated and faster-moving than ever.
In 2026, zero trust will be less about conceptual frameworks and more about operational architecture, especially within the LAN. Enterprise networks will enforce identity, segmentation, and policy as continuous behaviours rather than scheduled tasks. The LAN itself will become intelligent and adaptive, managed as a service where AI continuously verifies trust, optimises performance, and mitigates anomalies.
The market is responding accordingly. The global zero trust architecture market size was more than USD 30.63 billion in 2025 and is anticipated to grow at a CAGR of more than 16.8%, reaching USD 144.74 billion by 2035. Gartner estimates that 60% of companies will consider Zero Trust as a security starting point by 2025.
This isn’t a niche technology trend. It’s the new baseline.
The 7 Pillars of Zero Trust, Explained Simply
CISA, NIST, and leading security frameworks agree on seven foundational pillars that a mature Zero Trust architecture addresses. Think of these as the seven walls of your new security castle, except this castle is distributed, intelligent, and never fully open.
Pillar 1: Identity
Identity is the new perimeter. The single constant in all zero trust journeys is that they start with the subject’s identity. This means every user, employee, contractor, partner, or service account, must have a verified, managed digital identity.
In practice, this means strong multi-factor authentication (MFA), single sign-on (SSO) systems, and identity governance policies that define who can access what. The multi-factor authentication (MFA) segment dominated the zero trust architecture market and accounted for a revenue share of over 87% in 2024. It’s the most universally adopted Zero Trust control, and for good reason: MFA alone blocks the vast majority of credential-based attacks.
Pillar 2: Devices
Every device that connects to your network, laptop, phone, tablet, IoT sensor, is a potential attack vector. Zero Trust requires continuous visibility into device health. Is the device compliant with security policies? Is it running the latest patches? Has it been flagged for unusual behaviour?
Endpoint Detection and Response (EDR) tools form the backbone of device-level Zero Trust controls. The goal: if a device is compromised, that compromise should be detected and contained before it spreads.
Pillar 3: Network
Traditional network security drew a line between “inside” and “outside.” Zero Trust replaces this with microsegmentation, dividing the network into small, isolated zones so that even if an attacker gains access to one segment, they cannot move laterally to others.
ZTA uses granular network segmentation to restrict access to only the specific resources needed, significantly reducing the blast radius of a breach. For organisations in Singapore’s financial services sector, or UAE’s banking and fintech industry, microsegmentation is increasingly becoming a regulatory expectation, not just a best practice.
Pillar 4: Applications and Workloads
Applications, whether on-premises, SaaS, or cloud-native, must be secured at the application layer, not just the network layer. This means continuous monitoring of application behaviour, API security, and ensuring that only authenticated, authorised requests are processed.
Software-Defined Perimeters (SDPs) and Secure Access Service Edge (SASE) technologies are increasingly used here, providing dynamic, identity-based access to applications regardless of where users are connecting from.
Pillar 5: Data
This is what attackers actually want. Data-centric Zero Trust means classifying your data by sensitivity, encrypting it in transit and at rest, and applying access controls that ensure only the right people can read or move sensitive information.
Effective Zero Trust implementation requires understanding the current security tools and infrastructure, critical data and systems, risk tolerance, regulatory commitments, and business goals. For organisations handling personal data under India’s DPDPA, UAE’s data protection frameworks, or Singapore’s PDPA, this pillar directly supports compliance.
Pillar 6: Visibility and Analytics
Zero Trust without visibility is impossible. You need to see everything happening across your environment, every login attempt, every file access, every API call, every network connection, and you need the ability to detect anomalies in real time.
ZTA emphasises real-time monitoring, telemetry, and analytics across the environment. This enables quicker detection of anomalies and reduces the impact of breaches. Security Information and Event Management (SIEM) systems and AI-powered threat detection tools power this pillar.
Pillar 7: Automation and Orchestration
Manual security processes cannot keep pace with modern threats. Zero Trust architecture relies on automation to enforce policies consistently, respond to threats instantly, and adapt access controls dynamically based on changing context. An effective Zero Trust Architecture incorporates technologies that analyse user behaviour and other data to observe real-time events and proactively orient network defences.
Zero Trust vs. Traditional Security: The Honest Comparison
| Traditional Perimeter Security | Zero Trust Architecture | |
| Trust model | Trust inside the network | Trust nothing by default |
| Access control | Network position-based | Identity and context-based |
| Verification | One-time at login | Continuous throughout session |
| Visibility | Limited internal view | Full telemetry across environment |
| Breach response | Detect and respond | Assume and contain |
| Cloud compatibility | Poor | Built for cloud-first environments |
| Remote work | VPN-dependent | Natively distributed |
The traditional model made sense when everyone worked in the same office, on the same network, using the same company devices, and all data lived on on-premises servers. None of those conditions apply to most organisations in 2026.
The Business Case: What Zero Trust Actually Saves You
Zero Trust isn’t just a security conversation. It’s a business continuity conversation.
Adopting Zero Trust has been linked with significantly reducing the cost of data breaches, by around $1 million less on average. That is a compelling figure for any CIO or CFO: an architecture that can save real money by avoiding breach fallout. Moreover, about 59% of companies believe Zero Trust helps ensure business operations continue even under attack.
Based on Statista’s survey results, 61% of companies said adding zero trust segmentation in support of cloud security helps improve digital trust and strengthen cyber resilience.
For organisations in Asia Pacific, the fastest-growing region for Zero Trust adoption, the case is particularly compelling. Asia Pacific is likely to emerge as the fastest-growing regional market for Zero Trust, with digital transformation journeys of organisations in countries like China and India accelerating adoption.
In Singapore, where 36% of online adults are likely to share more personal data with tech companies they trust, demonstrating Zero Trust-backed security can directly drive customer confidence and revenue. But in the UAE, where Vision 2031 and the Dubai Digital Economy Strategy are accelerating cloud adoption across industries, Zero Trust provides the security foundation that makes that acceleration safe. In India, where the Digital Personal Data Protection Act (DPDPA) is reshaping how organizations handle citizen data, Zero Trust’s granular access controls and audit trails directly support compliance and reduce the legal exposure that comes with non-compliance.
Your Zero Trust Roadmap: Where to Start
Here is the practical reality: you don’t implement Zero Trust in a week. It’s a journey, not a purchase. But the journey has a clear starting point, and it doesn’t require a complete infrastructure overhaul on day one.
Achieving a true state of Zero Trust is not straightforward. Effective change management policies are essential for a successful Zero Trust implementation. This includes clear communication, comprehensive training, phased implementation, user feedback mechanisms, and cross-functional collaboration.
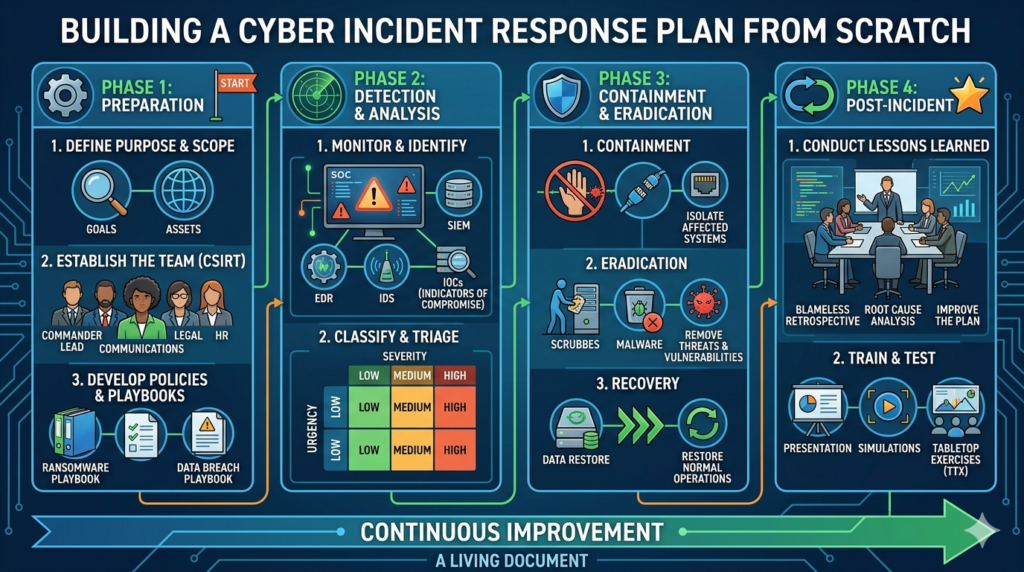
Stage 1: Identify and Prioritise (Weeks 1–4) Map your critical data, systems, and users. Ask: what are we protecting? Who needs access to what? Where are our biggest gaps? This discovery phase is essential, you can’t protect what you can’t see.
Stage 2: Strengthen Identity (Months 1–3) Deploy MFA across all accounts. Implement single sign-on (SSO). Audit privileged accounts and remove unnecessary access. This alone reduces your risk dramatically and is the foundational step every Zero Trust framework recommends.
Stage 3: Segment Your Network (Months 3–6) Begin microsegmentation. Separate critical systems from general network access. Ensure that a breach in one area cannot automatically cascade to everything else.
Stage 4: Secure Devices and Endpoints (Months 4–8) Deploy endpoint protection that gives you visibility into device health. Establish policies that restrict access from non-compliant or unmanaged devices.
Stage 5: Monitor, Detect, Respond (Ongoing) Implement continuous monitoring. Use SIEM and AI-powered analytics to detect anomalies. Build and test an incident response plan. Zero Trust is not a destination, it’s a continuous operational posture.
Begin with identity, adopt MFA, apply segmentation, use the zero trust maturity model, and build gradually across all pillars. This phased approach ensures you see tangible security improvements at each stage, without the paralysis of trying to do everything simultaneously.
The 2026 Reality: Zero Trust Is No Longer Optional
In 2026, the internal debate will no longer be “Should we do zero trust?” It will be “How fast can we remove each remaining pocket of implicit trust?” Teams that rely on legacy models will fall behind. Teams that build continuous verification into their architecture will see a smaller blast radius, faster detection, and more predictable operations.
Regulatory pressure is accelerating this shift. The US federal government issued a mandate in 2022 for all agencies to implement Zero Trust cybersecurity principles. In finance and healthcare, regulators are updating guidelines to emphasise access controls and continuous monitoring, core Zero Trust ideas, to protect sensitive data. Similar pressures are building across India, UAE, and Singapore as data protection legislation tightens and cyber incidents rise.
The organisations that thrive in this environment will not be those with the biggest IT budgets. They will be the ones that embrace the Zero Trust mindset: verify everything, trust nothing automatically, assume that you are under threat, and build systems that limit the damage when you are.
The fort is not secure. Build something smarter with Res-Q-Rity.