Most companies only think about this after a breach. Here’s how to mitigate that using a cyber incident response plan.
A cyberattack is no longer a question of if, it is a question of when. In 2023, the average cost of a data breach globally reached $4.45 million, the highest ever recorded, according to IBM’s Cost of a Data Breach Report. Yet a staggering 77% of organizations do not have a formal, consistently applied cybersecurity incident response plan. That gap is not a technical failure. It is a planning failure.
Building a cyber incident response plan (IRP) from scratch is not glamorous work. It does not show up on dashboards. It does not win sales deals. But when a ransomware attack locks your systems at 2 a.m. or an employee clicks a phishing link that exposes customer data, it is the single most important document your organization has ever written. This guide walks you through how to build one, even if you are starting from zero.
What Is a Cyber Incident Response Plan, and Why Does It Matter?
A cyber incident response plan is a documented, structured framework that tells your team what to do before, during, and after a cybersecurity incident. It defines roles, escalation paths, communication protocols, containment strategies, and recovery steps, all in one place.
The numbers make the case plain. Organizations with a formally tested cyber incident response plan save an average of $1.49 million compared to those without one, per IBM’s 2023 data. The mean time to identify and contain a breach is 277 days without a plan; with one, that window shrinks dramatically. In India, where cyberattacks on enterprises rose by 18% in 2023 (CERT-In), this is no longer an enterprise-only concern; mid-market companies and growth-stage startups are increasingly in the crosshairs.
An IRP is not the same as a disaster recovery plan (which focuses on restoring systems) or a business continuity plan (which keeps operations running). It sits upstream of both, activated the moment a potential threat is detected.
Step 1: Define Your Scope and Assets
You cannot protect what you have not mapped. The first step in building a cyber incident response plan is understanding what you are defending.
Start by creating an asset inventory. This includes hardware (servers, endpoints, IoT devices), software (applications, SaaS tools, APIs), data stores (databases, cloud storage, backup systems), and third-party integrations. For companies running ERP systems like SAP, this step is particularly critical, SAP environments often carry sensitive financial, customer, and operational data, and a breach at the integration layer can cascade across the entire business.
Next, classify your assets by criticality and sensitivity. A practical framework uses three tiers: Tier 1 (mission-critical, business-stopping if compromised), Tier 2 (important but recoverable within 24–48 hours), and Tier 3 (low impact). This classification will drive every prioritization decision in your response plan.
Finally, document your data flows. Where does sensitive data move? Who has access? What external vendors or APIs touch it? In 2023, 45% of breaches involved a third party or supply chain vector (Verizon DBIR). Your IRP must account for risk that enters through partners, not just internal systems.
Step 2: Build Your Incident Response Team (IRT)

A plan without people is just a PDF. Your Incident Response Team is the human engine of the entire operation, and it must be assembled before an incident occurs, not during one.
The core IRT should include the following roles:
- Incident Response Lead (IR Lead): Owns the response process end-to-end. Makes final calls on containment and escalation. Typically the CISO or Head of IT Security.
- Technical Responders: Security engineers and system administrators who execute containment, forensic investigation, and recovery tasks.
- Legal and Compliance Officer: Assesses regulatory obligations. In India, the Digital Personal Data Protection Act (DPDPA) 2023 mandates breach notification to the Data Protection Board. In the UK, GDPR requires notification to the ICO within 72 hours. In the USA, depending on the sector, HIPAA, SOC 2, or state-level laws like CCPA may apply. Legal must be in the room from hour one.
- Communications Lead: Manages internal communications, external PR, and customer notifications. Silence during a breach is not neutral, it actively erodes trust.
- Executive Sponsor: A C-suite owner (CEO or COO) who has decision-making authority for major actions, like taking systems offline, engaging law enforcement, or disclosing a breach publicly.
- Third-Party IR Retainer (optional but recommended): Many mid-sized organizations retain a specialist IR firm on a break-glass basis. Firms like Mandiant, CrowdStrike, or regional MSSP providers can be engaged within hours. Having a contract in place before an incident removes procurement friction at the worst possible moment.
Define a communication tree, who calls whom, in what order, using what channel. If your primary email is compromised, you need a backup communication method (Signal, a dedicated Slack workspace, or even a phone tree) already set up.
Step 3: Classify Incident Severity Levels
Not every security event is a five-alarm fire. Treating a phishing test failure the same as a ransomware infection will exhaust your team and create dangerous alert fatigue. Build a tiered severity model.
Severity 1, Critical: Active data exfiltration, ransomware deployment, complete system compromise. Full IRT activated within 1 hour. Executive sponsor notified immediately.
Severity 2, High: Unauthorized access detected but not confirmed to have exfiltrated data. Targeted phishing that compromised credentials. IRT lead and technical team activated within 4 hours.
Severity 3, Medium: Suspicious activity, failed intrusion attempts, malware detected and quarantined. Standard IT security response within 24 hours.
Severity 4, Low: Policy violations, anomalous but non-malicious user behavior, minor configuration errors. Logged and reviewed during normal business hours.
Clear severity definitions ensure that the right resources activate at the right speed, every time.
Step 4: Define the Six Phases of Response

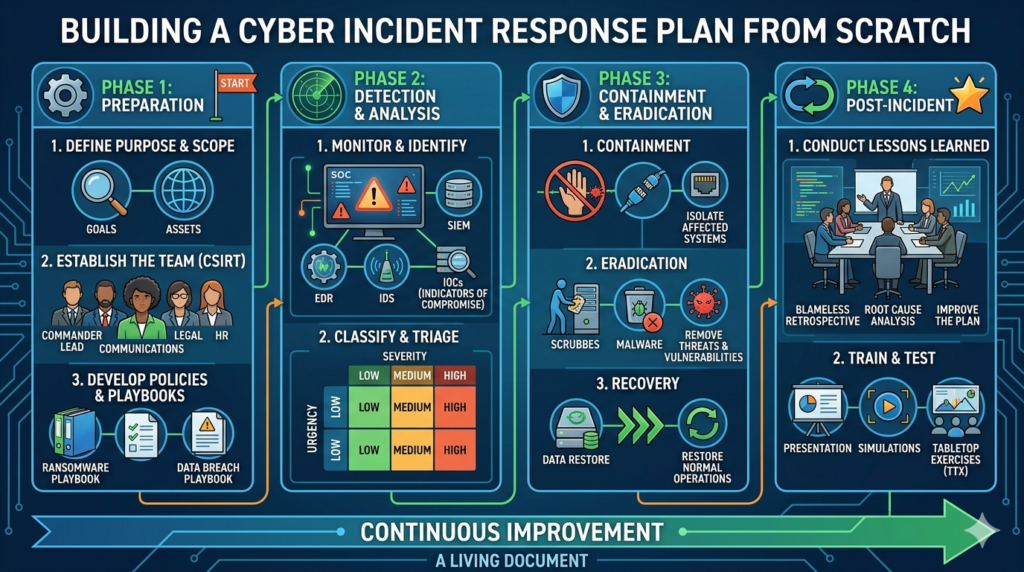
The NIST Cybersecurity Framework and SANS Institute both converge on a similar lifecycle for incident response. Your plan should be structured around these six phases.
Phase 1: Preparation
This is everything you do before an incident happens. It includes drafting the IRP itself, training staff, running tabletop exercises, setting up SIEM (Security Information and Event Management) tools, and establishing your communication protocols. Preparation is the only phase that is entirely within your control.
Phase 2: Identification
How do you know an incident has occurred? Detection sources include automated SIEM alerts, anomaly detection tools, employee reports, third-party notifications, or, in the worst case, a news article. Your plan should define what constitutes a “declared incident” and who has the authority to make that call. Globally, the average time to identify a breach is 204 days. The faster this phase is, the cheaper the outcome.
Phase 3: Containment
Stop the bleeding. Containment strategy depends on your severity classification. Short-term containment might involve isolating affected systems from the network, revoking compromised credentials, or blocking specific IPs. Long-term containment involves patching the exploited vulnerability, rebuilding affected systems on clean infrastructure, and restoring from verified backups. Document everything during this phase, your forensic log starts here.
Phase 4: Eradication
Remove the threat entirely. This means deleting malware, closing the attack vector, resetting all potentially compromised credentials, and scanning the environment to confirm the attacker has no remaining foothold. Do not skip this step in the rush to restore services. Organizations that move too quickly from containment to recovery often find themselves breached a second time within weeks.
Phase 5: Recovery
Bring systems back online in a controlled, phased manner. Validate integrity before restoring access. Monitor closely for any signs of reinfection. Recovery timelines should be pre-defined in your plan, for Tier 1 systems, what is your RTO (Recovery Time Objective)? 4 hours? 24 hours? Define it now, not during a crisis.
Phase 6: Lessons Learned
Within two weeks of incident closure, conduct a formal post-incident review. What happened? How was it detected? What slowed the response? What must change? This is where your IRP matures. Organizations that skip post-incident reviews repeat the same mistakes. According to Ponemon Institute, companies that conduct post-incident reviews reduce their average breach cost by 17% over time.
Step 5: Build Your Playbooks
Your IRP is the master framework. Playbooks are the operational instructions for specific threat scenarios. Think of the IRP as the constitution and playbooks as the specific laws.
Every organization should have playbooks for at minimum: ransomware attacks, phishing-driven credential compromise, insider threat incidents, DDoS attacks, and data exfiltration events. Each playbook should contain a threat description, indicators of compromise (IoCs), step-by-step response actions, containment decision tree, communication templates, and escalation checkpoints.
Playbooks are living documents. After every incident or tabletop exercise, update them. A playbook that was accurate 18 months ago may no longer reflect your current tech stack, team structure, or threat landscape.
Step 6: Address Regulatory and Notification Obligations

This is the area most organizations underestimate, and it is where legal and reputational exposure is highest.
In India, CERT-In requires organizations to report incidents within 6 hours of detection. The DPDPA 2023 adds data breach notification obligations to individuals and the Data Protection Board. Failure to comply can result in penalties of up to ₹250 crore.
In the UK, post-Brexit GDPR (UK GDPR) requires notification to the ICO within 72 hours if the breach poses a risk to individuals. Failure to notify carries fines of up to £17.5 million or 4% of global annual turnover.
In the USA, notification requirements vary by state and sector. HIPAA requires notification within 60 days for breaches affecting more than 500 individuals. California’s CCPA mandates notification “in the most expedient time possible.” The SEC now requires public companies to disclose material cybersecurity incidents within 4 business days of determining materiality.
Your IRP must include a regulatory checklist for each jurisdiction in which you operate. Your legal team should review and sign off on this section annually.
Step 7: Test, Train, and Update
A plan that has never been tested is a plan that will fail under pressure. Research by Ponemon shows that organizations that test their IRP at least twice a year experience breach costs that are 35% lower than those that do not test at all.
Testing takes three forms. Tabletop exercises are structured discussion-based walkthroughs, no systems are touched, but the team talks through how they would respond to a scenario. Simulation drills involve simulating specific attack vectors in a controlled environment. Full red team/blue team exercises have an internal or external team actively attempting to breach your systems while your security team responds in real time.
Schedule at minimum one tabletop exercise per quarter and one full simulation per year. Use the output of each exercise to update your IRP and playbooks.
Staff training matters equally. 95% of cybersecurity incidents are caused by human error (IBM). Your IRP is only as strong as the people executing it. Phishing simulations, security awareness training, and IR drills for non-technical staff (who are often the first line of detection) are non-negotiable elements of a functional plan.
The IR Plan Template: What to Include

A complete IR plan document should contain the following sections: executive summary and purpose, scope and asset inventory, IRT roster with contact information and alternates, severity classification matrix, the six response phases with phase-specific checklists, playbooks for top threat scenarios, regulatory notification obligations by jurisdiction, communication templates (internal, customer-facing, regulator-facing), post-incident review template, and a document version control log.
Keep the plan concise, readable, and accessible. The worst outcome is a 150-page document that no one reads and no one can navigate during an actual incident. A well-structured IRP can be 20–30 pages with supporting playbooks as appendices.
Final Thought: Preparation Is the Response
Every hour you spend building your incident response plan today is worth approximately $10,000 in breach-related costs avoided tomorrow, that is the direct math from IBM’s 2023 dataset, based on average containment time differentials. The companies that recover fastest from cyberattacks are not the ones with the biggest security budgets. They are the ones that treated preparation as a strategic function, not an afterthought.
Build the plan. Test it. Update it. Then hope you never need it, while knowing you are ready if you do.
Frequently Asked Questions
1. How long does it typically take to detect a cyberattack?
Detection timelines vary widely, but many organizations take months to identify a breach. In India, the average time-to-detection for fraud-related incidents can extend significantly, which increases financial and reputational damage. Faster detection depends on monitoring systems, employee awareness, and clearly defined escalation processes within the organization.
2. Why do attackers prefer email-based attacks over technical hacks?
Email-based attacks require less effort and lower cost while delivering high returns. Instead of breaking into systems, attackers exploit human behavior, trust, and urgency. A well-crafted email can bypass even strong technical defenses because it targets decision-making rather than infrastructure, making it one of the most effective attack methods today.
3. What is the biggest mistake companies make during an attack?
The most common mistake is skipping verification under pressure. Urgent requests, especially from senior executives, often lead employees to act quickly without confirming details. This breakdown in process, rather than a lack of technology, is what attackers rely on. A simple verification step could prevent most financial fraud incidents.
4. How important is having an incident response plan?
An incident response plan is critical because it defines what to do before, during, and after an attack. Organizations with a tested plan respond faster, reduce damage, and recover more effectively. Without one, teams react in confusion, which delays action and increases both financial loss and operational disruption.
5. Can companies fully recover from large-scale financial cyberattacks?
Recovery is often partial and depends on how quickly action is taken. Funds can sometimes be traced and frozen, but complete recovery is rare. Beyond financial loss, companies also face operational disruption, legal costs, and reputational damage. This is why prevention and early detection are far more effective than relying on recovery after an attack occurs.