Blog
Selected Articles
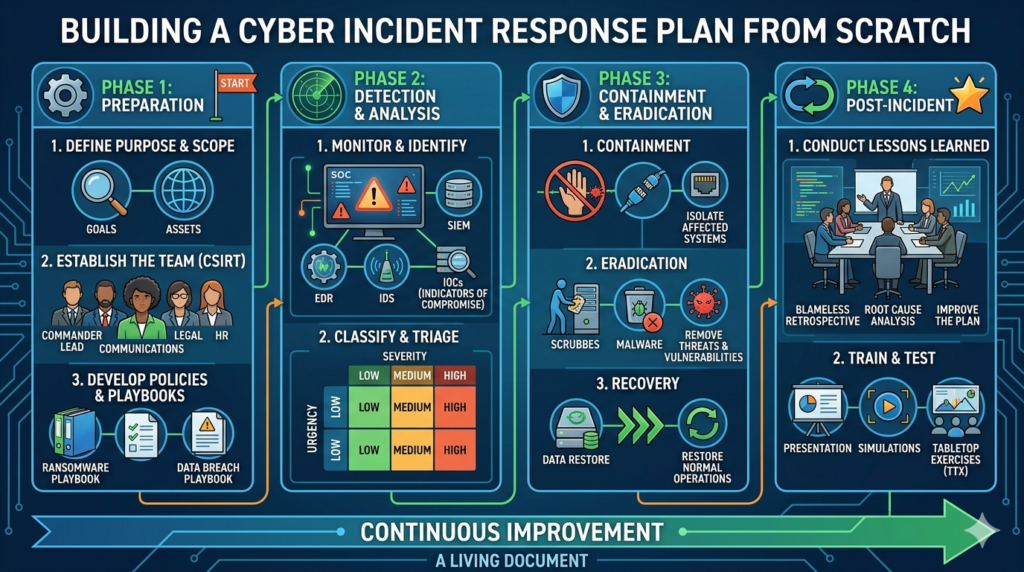
How to Build a Cyber Incident Response Plan from Scratch
Most companies only think about this after a breach. Here’s how to start before that. A cyberattack is no longer……

Inside a Real Phishing Attack That Hit Navi
A real company. A real attack. Numbers that will make your finance team sit up straight. When Navi Technologies Got……

10 Signs Your Network Has Already Been Breached
Silent breaches are the scariest. Are these warning signs already present in your network? Read this before your next Monday……

Zero Trust Architecture: A Beginner’s Roadmap
Picture a medieval castle. Thick walls. A drawbridge. A moat. Anyone inside those walls is trusted, they made it past……

Why SMEs Are the #1 Target for Ransomware in 2026
Most small business owners believe they’re too small to be targeted. The data says otherwise, and the stakes couldn’t be……

Managing Risks in Incident Response: A Comprehensive Approach
In the increasingly interconnected digital world, organizations face constant threats from cyber incidents that can cripple their operations, expose sensitive……

How to Make Cybersecurity Education and Awareness More Effective
In today’s digitally connected world, cybersecurity has become a critical issue for both individuals and organizations. Despite the increasing awareness……

Hackers’ Wishlist: The 5 Most Targeted Entry Points
In the digital age, cybercrime has reached an unprecedented level, with malicious actors exploiting a variety of techniques to infiltrate……

How to Get Your Organization Through the Residual Risk Phase
Risk management is a critical process in any organization, involving the identification, assessment, and mitigation of various threats that could……

India’s Critical Infrastructure Suffers Spike in Cyberattacks
India’s Critical Infrastructure Suffers Spike in Cyberattacks India, one of the world’s fastest-growing digital economies, has become increasingly vulnerable to……